- M3 Bitlocker Recovery Professional v.4.5 M3 Bitlocker Recovery Professional is the World's first Bitlocker recovery software to recover deleted files from Bitlocker encrypted drive, decrypt/recover data from damaged, corrupted, failed, crashed, lost or deleted Bitlocker encrypted partition.
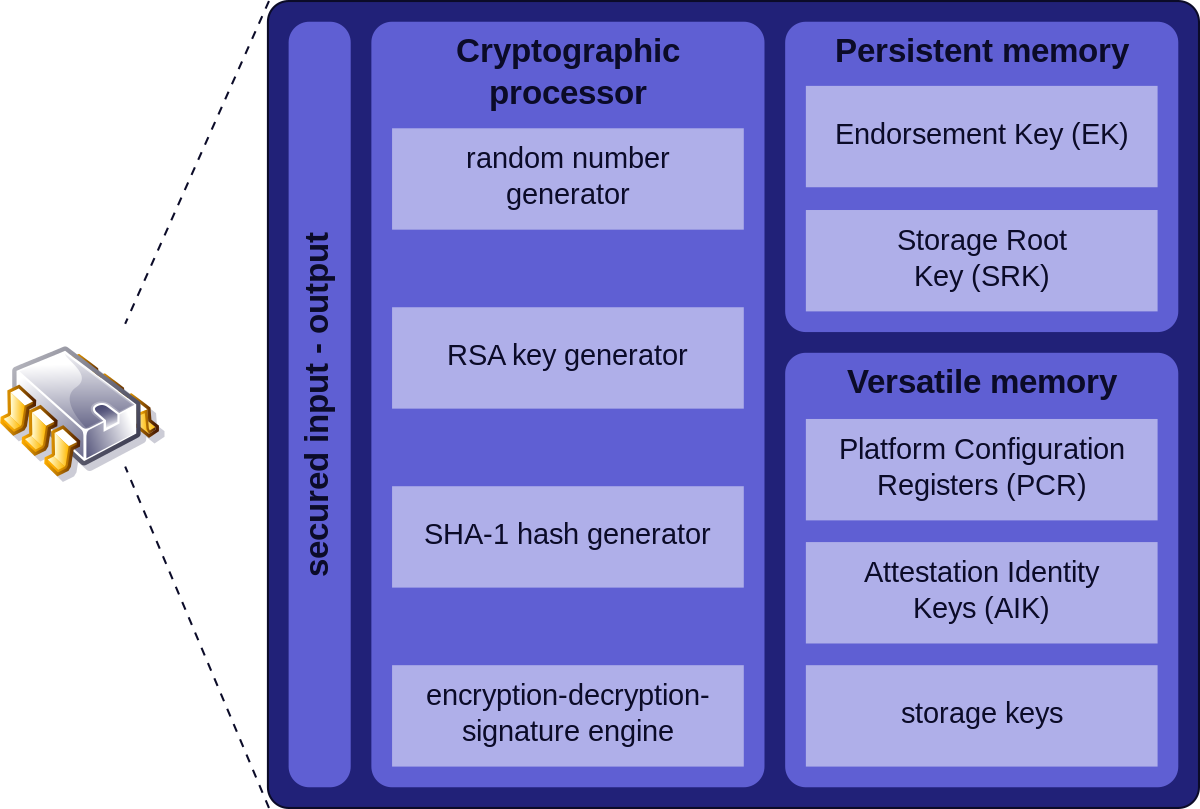
- The encryption key can be stored inside a Trusted Platform Module chip found in high end computer motherboards. Although there is not known Bitlocker backdoor most businesses will ask for a password recovery option, Bitlocker allows you to create a recovery key that can be printed or stored in external media.
Bitlocker Recovery Key Generator Software Downloads
The BitLocker feature of Windows is supposed to offer a degree of peace of mind that files are going to be secure -- but one expert points out that a simple key combo is all it takes to bypass the security feature.
A bug has been discovered in the way Windows 10 handles a Feature Update -- the installation of a new build of the operating system. By taking advantage of the bug, it is possible to access a Command Prompt and gain unrestricted access to the contents of the hard drive.
Windows Version M3 BitLocker Recovery is a professional BitLocker data recovery software. It can recover deleted or lost files from BitLocker encrypted drive after providing the password or 48-digit recovery key. Tutorial to recover data from BitLocker encrypted drive. M3 BitLocker Data Recovery is a BitLocker data recovery software which can help you recover data from BitLocker Encrypted Drive. Repair-bde can reconstruct critical parts of the drive and salvage recoverable data as long as a valid BitLocker password, recovery key, or startup key (.BEK file) is used to decrypt the data. To recover a damaged OS drive with the BitLocker Repair Tool, the OS drive will need to be connected to another PC if you are not multi-booting with.
The reason for this is that BitLocker is disabled during the update process, as security expert Sami Laiho points out. He reveals that exploiting the bug takes nothing more than pressing Shift + F10 during the upgrade and you can then access the Command Prompt in the Windows PE (Preinstallation Environment) used during the upgrade.
While exploiting the bug -- which, we are assured, Microsoft is 'working on' -- does require access to a computer, it is still a concern. Laiho says:
The real issue here is the Elevation of Privilege that takes a non-admin to SYSTEM (the root of Windows) even on a BitLocker (Microsoft's hard disk encryption) protected machine. And of course that this doesn't require any external hardware or additional software.
So what can you do to keep your computer secure? Well, until a fix is released for the problem, there are limits to the protective steps you can take, but Laiho offers the following advice:
- Don't allow unattended upgrades
- Keep very tight watch on the Insiders
- Stick to LTSB version of Windows 10 for now
Photo Credit:Anton Watman / Shutterstock.com
Category: «Security», «Software», «Tips & Tricks»
10 2 - 12
Investigators start seeing BitLocker encrypted volumes more and more often, yet computer users themselves may be genuinely unaware of the fact they’ve been encrypting their disk all along. How can you break into BitLocker encryption? Do you have to brute-force the password, or is there a quick hack to exploit?
We did our research, and are ready to share our findings. Due to the sheer amount of information, we had to break this publication into two parts. In today’s Part I, we’ll discuss the possibility of using a backdoor to hack our way into BitLocker. This publication will be followed by Part II, in which we’ll discuss brute-force possibilities if access to encrypted information through the backdoor is not available.
Exploiting the Backdoor
We love tools. We have lots of them. Some tools we have will seemingly do the same job, while achieving the result via different paths. One question we’re asked a lot is why ElcomSoft has two different tools for breaking BitLocker encryption. Really, why?
Bitlocker Recovery Key Generator Software Free
We offer Elcomsoft Forensic Disk Decryptor to decrypt BitLocker volumes, and we offer Elcomsoft Distributed Password Recovery to break BitLocker passwords. (EDPR for short). We also have a small tool called Elcomsoft Disk Encryption Info (part of Distributed Password Recovery) to display information about encrypted containers. What are these tools? What do they do, exactly, and which one do YOU need in YOUR investigation? It is time to unveil the secrets and shed light on these questions.
The Tools
Elcomsoft Forensic Disk Decryptor and Elcomsoft Distributed Password Recovery. Which one should you choose for your investigation?
To put it briefly, Elcomsoft Forensic Disk Decryptor and Elcomsoft Distributed Password Recovery use different approaches when gaining access to encrypted volumes. The choice primarily depends on whether or not you have certain bits of information extracted from the computer’s volatile memory (RAM). If you do, your job can become much easier.
Elcomsoft Forensic Disk Decryptor is designed to instantly decrypt disks and volumes using the decryption key extracted from the computer’s volatile memory (RAM). In addition, you can decrypt for offline analysis or instantly mount BitLocker volumes by utilizing the escrow key (BitLocker Recovery Key) extracted from the user’s Microsoft Account or retrieved from Active Directory. Elcomsoft Forensic Disk Decryptor works with physical disks as well as RAW (DD) images.
Elcomsoft Distributed Password Recovery, on the other hand, attempts to break (recover) passwords to disks and volumes by running an attack.
Did you get the impression that the two tools complement each other? We’ll be happy if you buy both, but in fact you’ll be probably using just one. The two tools attack different links in the security chain of BitLocker, PGP and TrueCrypt. We’ll discuss the two methods separately.
Let’s start with Elcomsoft Forensic Disk Decryptor. When we launched this product in 2012, we posted this article: ElcomSoft Decrypts BitLocker, PGP and TrueCrypt Containers. The publication describes the tool’s functionality and unique features. Since then, the world has witnessed the end of TrueCrypt, whereas PGP and BitLocker continue to exist with several updates (including a big security update for BitLocker in Windows 10 build 1511, the “November Update”). Today, Elcomsoft Forensic Disk Decryptor is in even greater demand than three years ago.
Elcomsoft Forensic Disk Decryptor has the ability to extract the original decryption key stored in the computer’s volatile memory (RAM). By extracting this key from a memory dump, the tool can use it to either mount the encrypted volume for on-the-fly access to files and folders (which is instant), or for decrypting the whole disk or volume at once in order to work with decrypted content (slower but bearable).
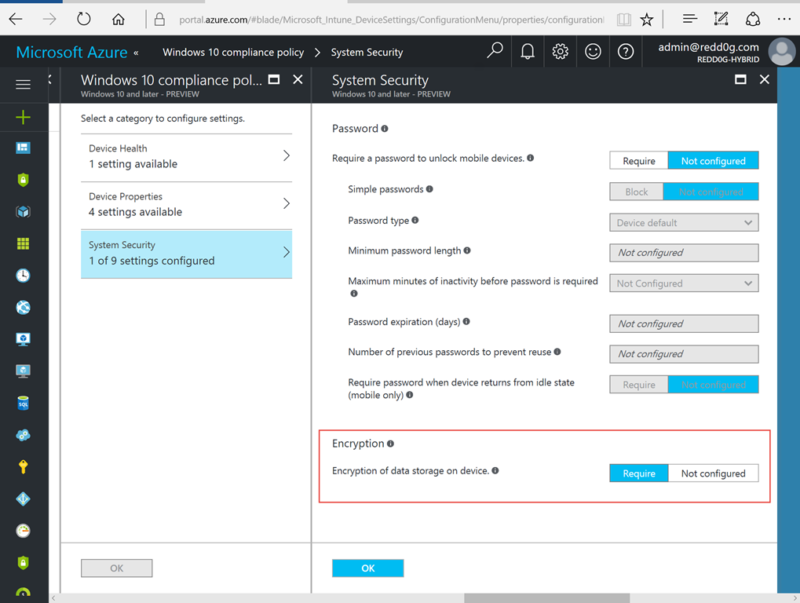
IMPORTANT: Use Elcomsoft Forensic Disk Decryptor to acquire volumes encrypted with BitLocker Device Protection. BitLocker Device Protection is a whole-disk encryption scheme that automatically protects certain Windows devices (such as tablets and ultrabooks equipped with TPM 2.0 modules) when the user logs in with their Microsoft Account. BitLocker Device Protection does NOT employ user-selectable passwords, and CANNOT be broken into by brute forcing anything. In certain cases, BitLocker escrow keys (BitLocker Recovery Keys) can be extracted by logging in to the user’s Microsoft Account via https://onedrive.live.com/recoverykey. The latest version of Elcomsoft Forensic Disk Decryptor (the one we’ve just released) has the ability to use these keys in order to decrypt or mount BitLocker volumes.
The moment the encrypted disk is mounted into the system (which is when you enter the password to access it, or provide the smart card, or use any other type of authentication), the system stores the encryption key in order to simplify accessing encrypted data. And since these keys are kept in system memory (regardless of the authentication method used), one can attempt to extract them.
There are several ways to get the original keys out of the system:
- Sometimes, the decryption key can be extracted from the hibernation file, which is created when the system is hibernated. The system dumps an image of the computer’s RAM into a file when entering hibernation. Windows uses the hiberfil.sys file to store a copy of the system memory. However, some systems (e.g. slates with Connected Standby or Modern Standby, which are very likely to employ BitLocker Device Protection) may not use hibernation at all (Connected Standby is used instead until the system reaches a very low power state, after which it can either hibernate or shut down). More information how to enable or disable hibernation is available at http://support.microsoft.com/kb/920730.
- You can also attempt imaging a ‘live’ system using one of the many memory dumping tools (administrative privileges required). The complete description of this technology and a comprehensive list of tools (free and commercial) is available at http://www.forensicswiki.org/wiki/Tools:Memory_Imaging. We recommend MoonSols Windows Memory Toolkit (paid tool, no demo version, pricing on request with no contact form available) or Belkasoft Live RAM Capturer (free, immediately downloadable, minimal footprint and kernel-mode operation on 32-bit and 64-bit systems).
- The last option is available on certain systems equipped with a FireWire port. It is possible to directly access the memory of a computer (even if it is locked) via a FireWire port. There are several tools that can acquire memory using this technology, e.g. Inception (yes, it’s “that Python tool”).
If you are able to image the computer’s volatile memory while the encrypted disk is mounted, or if you have access to the system’s hibernation file, you can use Elcomsoft Forensic Disk Decryptor to analyze the memory image or hibernation file, detect and extract the decryption keys. You can then use these keys to have Elcomsoft Forensic Disk Decryptor decrypt the volume or mount it.
We can break down the whole job to just three steps:
- Obtain a memory dump or grab the hibernation file
- Analyze the dump and find encryption keys
- Decrypt or mount the disk
It’s worth mentioning that looking for a key can be time-consuming. Specifying the types of encryption keys (if you know what algorithm has been used) can save you a lot of time. If you don’t know what type of encryption was used, just select all of them.
Once the keys are discovered, the tool displays them and allows you to save them into a file. You can save multiple keys of different types into a single file.
Having the decryption keys, you can proceed to decrypting the disk. Specify the type of the crypto container, select the file with decryption keys, and click Next.
If proper encryption keys are there, the tool will prompt you to either do full decryption (creating a raw image that can be mounted or analyzed with a third-party tool), or mount the volume into the current system. Mounting is implemented via ImDisk virtual disk driver (installed with Elcomsoft Forensic Disk Decryptor). Normally, you won’t need to change any settings and simply press the Mount button:
As you can see, this method is convenient and efficient. Whether or not you can use it depends entirely on the possibility of acquiring the decryption key from the computer’s RAM image. Please have a look at Elcomsoft Forensic Disk Decryptor product page to learn more on acquiring the decryption keys.
You are also welcome to check a quick EFDD video tutorial made by Sethioz.
What if you don’t have access to the decryption key? Elcomsoft Distributed Password Recovery uses a completely different approach. We’ll dwell on this in the second part of this article. Stay tuned and visit us in a day or two for the second part of this reading!
10 2 - 12